Fraud, Waste and Abuse Defined by the Oregon Secretary of State
Fraud
A dishonest and deliberate course of action that results in the obtaining of money, property, or an advantage to which state employees or an official committing the action would not normally be entitled. Intentional misleading or deceitful conduct that deprives the state of its resources or rights. There are three categories of fraud: financial statement fraud, misappropriation of assets, and corruption.
Examples:
- Falsifying financial records to cover up theft
- Theft or misuse of state money, equipment, supplies or other materials
- Intentionally misrepresenting the costs of goods or services provided
- Falsifying payroll information
- Use of state equipment or property for personal gain
- Submitting false claims for reimbursements
- Soliciting or accepting a bribe or kickback
- Intentional use of false weights or measures
The Fraud Triangle
By reducing opportunity, greater presssure and rationalization is needed to commit fraud.
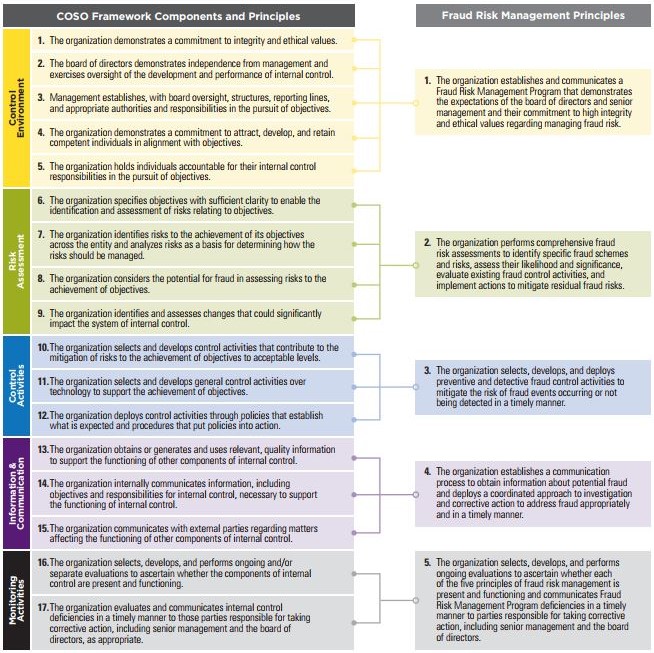
COSO Fraud Risk Management Principles (2016)
"How might a fraud perpetrator exploit weaknesses in your system of controls?
How could a perpetrator overrride or circumvent controls?
Who might have a motive or incentive to commit fraud?
Given identified fraud risks, which controls are critical to preventing fraud?
What controls might be subject to fraudulent attacks?"
- COSO "Fraud Risk Management Guide", 2016




